Published
Weekend Reading — #WFH
JOE.co.uk #WFH
Design Objective
How a Facebook Designer Thinks "Julie Zhuo describes how the development of new features starts with three questions: What people problem are we solving? How do we know it’s a real problem? And how will we know if we’ve solved it?" I recommend taking 35 minutes out of your day to watch this talk.
Start With A Goal. The Backlog Will Follow Goal driven development:
Out of that goal, a small feature list almost wrote itself. This is how planning should work; not with backlogs of feature requests, but with customers and developers closely collaborating to achieve goals.
It's similar in many ways to how TDD should work - in fact, arguably, it is TDD (except we start with business tests).
The magic of microcopy Delight is in the details.
The Ladder of Evidence: Get More Value From Your Customer Interviews and Product Experiments TL;DR Ask for specific stories about the past to generate better insights.
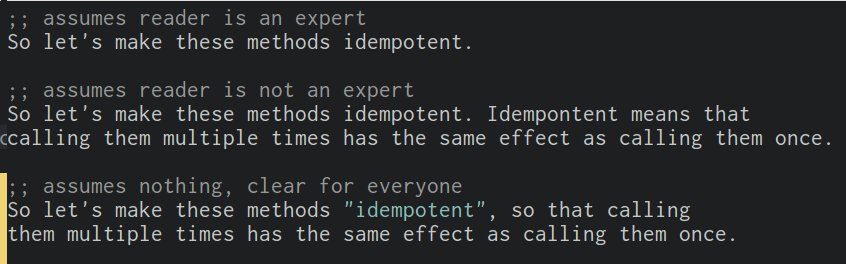
Technical writing pro-tip. You can be accessible to people of varying skill level without dumbing things down or being condescending.
The little-known iPhone feature that lets blind people see with their fingers A quick look at how blind people use VoiceOver to navigate the iPhone UI.
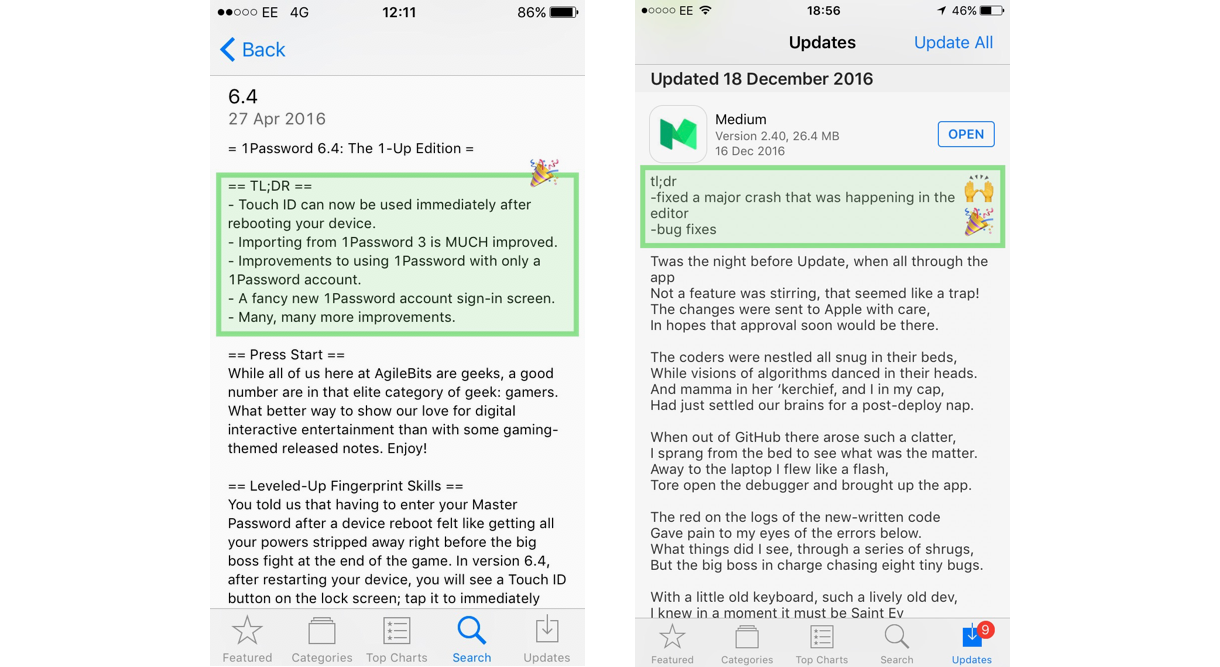
As a Designer I want better Release Notes Tips to help you write better release notes.
Best Practices for Search Results If you're working on a search UI, here are 10 things to help you improve the search results UX. And please "Don’t erase users’ query after they hit Search button."
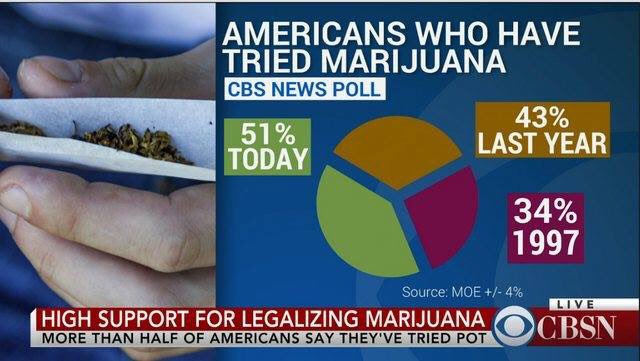
\m/ (-_-) \m/ "Remember kids, never do data visualization while under the influence."
Tools of the Trade
Driving user growth with performance improvements If you like optimizing the performance of web apps, you'll love this story:
The result of rebuilding our pages for performance led to a 40 percent decrease in Pinner wait time, a 15 percent increase in SEO traffic and a 15 percent increase in conversion rate to signup. Because the traffic and conversion rate increases are multiplicative, this was a huge win for us in terms of web and app signups. In 2016, this was our team’s biggest user acquisition win.
Round error issue -> produce money for free TL;DR Do not use floating point for money.
sindresorhus/fkill-cli Command line tool to find and kill a process with auto complete.

Linting HTML using CSS This CSS stylesheet will help you spot missing attributes, broken links, unaccessible images, and more.
Thou shalt not depend on me Analysis of outdated JavaScript libraries on the web. When was the last time you updated your client-side JavaScript dependencies?
The key lesson from our serverless migration How to go all in with AWS features, storage, security, etc. But also, vendor lock in.
AudioSet A large-scale dataset of manually annotated audio events to feed your machine learning models.
Next-generation IP spec edges closer to reality Credit to wayback_exe for picking up this forward looking article from December 1996.
Unexpected learnings from the CIA leak The banality of developing software at the intelligence agency: complaining about too much process, code reviews, copying code from StackOverflow, and JIRA. Also, lots of memes.
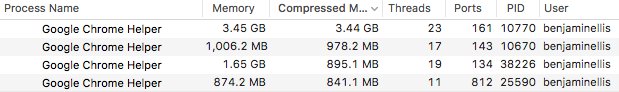
Benjamin Ellis Moore's law:
Google Chrome on my mac is currently consuming more memory than existed on the entire planet when I wrote my first programme…
Lingua Scripta
The Real Story Behind ECMAScript 4 The story of ECMAScript 4, what exactly happened behind the scenes, and why it never materialized.
Lines of Code
Vesa Karvonen "Never be impressed by complexity."

Manisha Agarwal Related:
"It's good to write clever code"
Writing clever code is a form of 'expensive signalling', like wearing expensive but easily damaged clothes
“Without requirements or design, programming is the art of adding bugs to an empty text file.” - Louis Srygley
The Practical Dev Too soon:
Architectural
"Surprise is one of the most expensive things you can put into a software architecture”
— Adam Tornhill
Author of Your Code as a Crime Scene
Serverless Architecture: Five Design Patterns The five predominant usage patterns of AWS Lambda serverless service, according to AWS Solution Architect Cassandra Bonner.
Redundancy does not imply fault tolerance An analysis of distributed storage reactions to single errors and corruptions. Watch as a Redis cluster loses all your data due to a trivial and expected disk failure.
Bud Caddell "Borrowing from @snowded to help teams align their tasks w/ the right approach."

Locked Doors
Do Not Return Calls or Texts From These Area Codes--It May Be a Scam If you don't recognize the phone number, a) do not pick up the phone!, and b) do not call back, c) if they left a voice message, Google the number before calling.
WikiLeaks CIA cache: Fool me once So a lot of people suddenly became aware the CIA is a spy agency. And no, the CIA did not wide-scale hack Signal or WhatsApp, end-to-end encryption still works. What they can do, if they gain physical access to your iOS/Android device, is install a listening bug and monitor everything you do.
The Life and Times of Zero-Day Vulnerabilities and Their Exploits Interesting tidbits from this report:
- Zero-day exploits and their underlying vulnerabilities have a rather long average life expectancy (6.9 years). Only 25 percent of vulnerabilities do not survive to 1.51 years, and only 25 percent live more than 9.5 years.
- For a given stockpile of zero-day vulnerabilities, after a year, approximately 5.7 percent have been publicly discovered and disclosed by another entity.
- Once an exploitable vulnerability has been found, time to develop a fully functioning exploit is relatively fast, with a median time of 22 days.
Look, I'm not saying ATMs are trivial to hack, just that lots of them seem to run Doom okay. Infer what you will 😏

Peopleware
We are all each other’s emergency contact. We just don’t know it yet. "It was the highlight of my week. Because I was able to connect with someone who needed it, at the moment that they needed it."
What it feels like to be an open-source maintainer "In a sense, these GitHub notifications are a constant stream of negativity about your projects. Nobody opens an issue or a pull request when they’re satisfied with your work."
Running a business with boobs: the things I never say Dealing with everyday sexism in tech:
I’ve seen dudes being hailed as ambitious simply for quitting their cushy day jobs, yet it’s surprisingly common for women to be questioned on whether they are ambitious “enough.” Stop questioning the ambition level of women in business.
Martin R. Schneider Related. Read the entire thread:
We did an experiment: For two weeks we switched names. I signed all client emails as Nicole. She signed as me.
Folks. It fucking sucked.
How the Design of Hotel Rooms Makes Housekeepers Invisible "Making housekeepers’ work invisible has been an objective of the hotel industry since its beginnings in the 19th century."
Techtopia
The 9-1-1 Paradox This article hides a broader lesson about systems engineering:
Ironically enough, the aging systems first responders use to communicate with one another may offer a layer of protection in such a scenario. “Those radio systems typically use old-school technology,” Forgety said. Which makes them safe from computer-age attacks. Then again, he added, “nothing is impossible.”
Car salesman: and it has a back up camera
Me: Cool, where's the main camera?
Cs: Sorry no this is for backing up
Me: Ah, to the cloud
Cs: no
The Onion "Jumbled Nest Of Cords Makes Move To Third New Apartment"

None of the Above
These Folding Landscape Photos Will Mess With Your Brain Trippy.
![]()
Margaret Atwood on What ‘The Handmaid’s Tale’ Means in the Age of Trump "Back in 1984, the main premise seemed — even to me — fairly outrageous."
Lindsey B "Hippos are way more dangerous than many people think watch as this one attacks a human :3"
Meet Silicon Valley's Secretive Alt-Right Followers Mother Jones digs into the racist tech underworld.
Thirteen thousand, four hundred, fifty-five minutes of talking to get one job One developers's job hunt, quantified and beautifully visualized.
Napflix "Siesta Video Platform." Boring videos to help you fall asleep.
Trump, Putin, and the New Cold War Fantastic write up by the New Yorker.
10 Apps That Will Help You Become A Better Investor This Year Round up of newish, user friendly, and budget friendly tools for everyday investors.
Ncore Retro Mechanical Keyboard


