Published
Weekend Reading — We've come full circle

Ana Milicevic "We've come full circle ⭕"
Design Objective
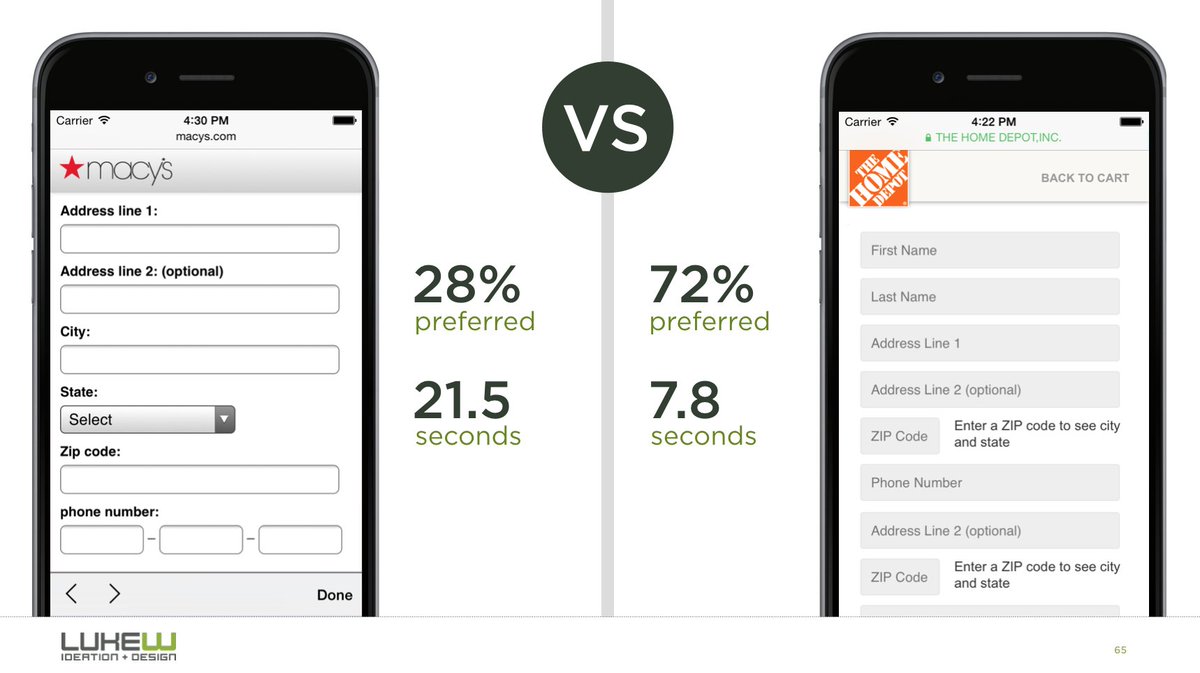
Luke Wroblewski "not only do people prefer not entering city/state, they’re 93% faster when using ZIP to get both automatically."
2017 state of email report (PDF) 80 pages of what's new, what changed, and what email clients are still stuck in the past.
Tools of the Trade
RegexHQ Community-driven collections of RegExp patterns and tools: twitter mentions, credit card numbers, usernames, POSIX paths, and more.
Preload, Prefetch And Priorities in Chrome TL;DR preload asks the browser to fetch the resource, prefetch hints it might be fetched in the future. But, of course, there are nuances and gotchas, so check out the article.
Chromium policy on JavaScript dialogs Unfortunately, the alternatives are an unsupported HTML element, or the annoying Notifications API:
alert()/confirm()/prompt()dialogs are being changed. Rather than being app-modal, they will be dismissed when their tab is switched from. (Safari 9.1 already does this.)
Scrolling on the web: A primer There's nothing simple about handling scroll events:
Developers should also use passive event listeners whenever possible, with feature detection to avoid compatibility issues. Using Pointer Events (there is a polyfill) and “scroll” listeners are also surefire ways to prevent unintentional scroll-blocking.
Königsberg: Seven Small Bridges, One Giant Graph Problem Challenges, graphs, Euler, and shifting perspectives.
This WE I learned that web apps rendering HTML on the server are “the legacy way”. Yep, they are built to last.
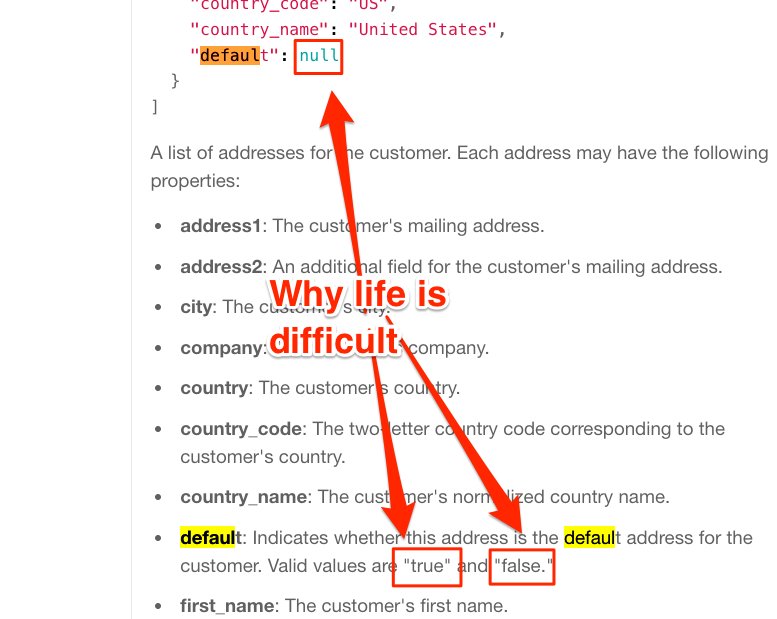
People sometimes ask me: "Mike, why is programming hard? It's just telling the computer what to do?" I show them this screenshot
Lingua Scripta
myshov/function_invocation.js All the different ways to invoke a function in JavaScript.
Unhandled Promise Rejections in Node.js Learning to live with unhandledRejection.
brockwhittaker/BitArray.js A memory efficient implementation of bit flag arrays in JavaScript, using Uint32Array.
Lines of Code
Principle of reasonable expectations Another way to think about naming (variables, functions, etc):
Another useful thing that this principle surfaces is that if something provides no reasonable expectations, then it is a violation of the principle. Consequently, naming functions as for example handleTriggerFailed will violate the principle since there is not much that the reader of the code can infer from that method name.
A lack of automated tests is not what causes defects... a lack of system understanding is. Tests let us automate part of our understanding.
Rod Vagg Dot Com "This guy is a software engineer, you can tell by his awesome estimation skills"

Peopleware
Suz Hinton Great thread, on what it means to be a senior engineer:
If you're a senior engineer, you have a responsibility to your team; not just getting to code on whatever you want/changing architecture.
The hero worship of successful people is just survivorship bias in action. Out of a population of people flipping coins, we (after the fact) find the ones who flipped heads 10 times in a row and fawn over them, asking them how they became such great coin flippers and what we can do to improve our coin flipping skills. See also: Good To Great or any similar business book.
anna borges "good news everyone the search is over"

Locked Doors
A Method for Obtaining Digital Signatures and Public-Key Cryptosystems In which Alice and Bob, are first introduced to the world. They just celebrated their 40th birthday.
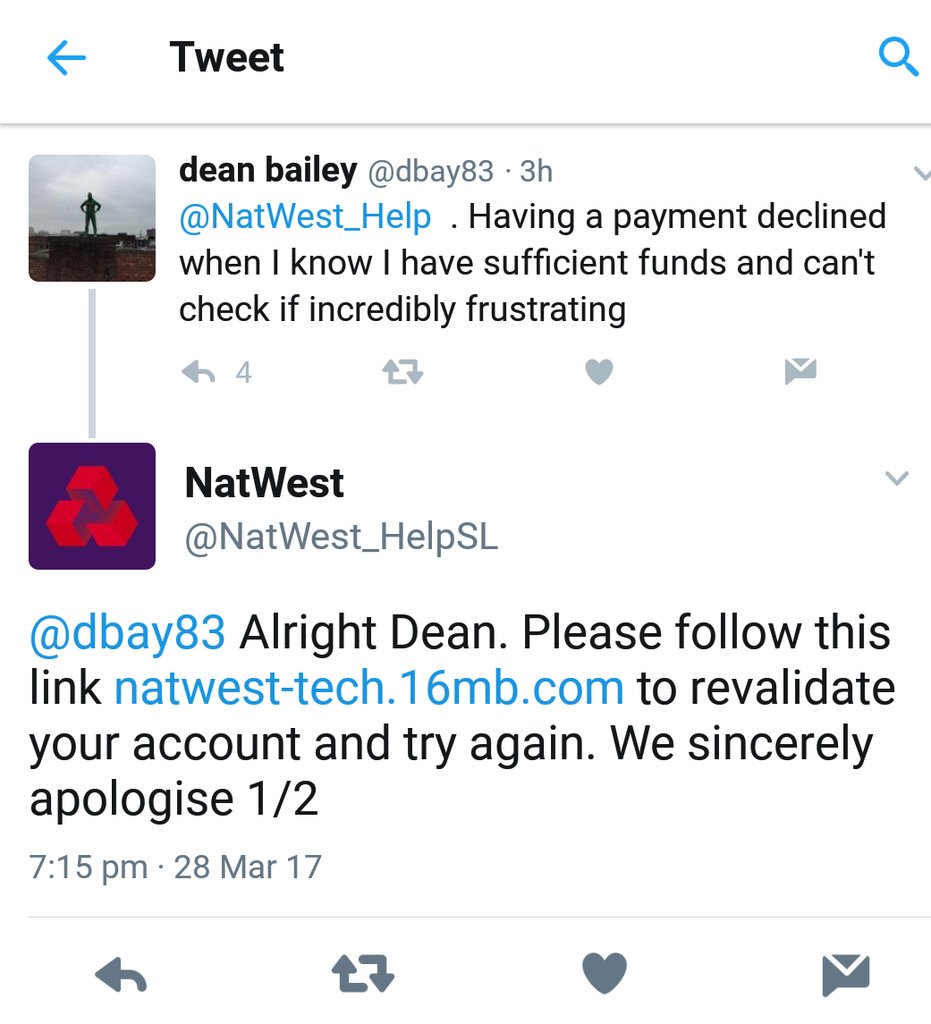
Twitter Phishing Scam Targeting Customers of Barclays, Other Major UK Banks Customer tweets at bank, requesting help. Attacker responds from a legitimately looking Twitter account, sends customer link to a bogus support page.
Smart TV hack embeds attack code into broadcast signal—no access required "The proof-of-concept exploit uses a low-cost transmitter to embed malicious commands into a rogue TV signal … By exploiting two known security flaws in the Web browsers running in the background, the attack was able to gain highly privileged root access to the TVs."
Automatically Inferring Malware Signatures for Anti-Virus Assisted Attacks (PDF) Clever way of recruiting anti-virus software to help the attacker:
We proceed to demonstrate the threat of anti-virus assisted attacks and feasibility of implanting malicious markers in three different scenarios: 1) covering up password guessing, 2) deleting a user’s emails and 3) facilitating web-based attacks by removing browser cookies. For each scenario we choose a different anti-virus product to demonstrate the generality of the approach.
Identifying HTTPS-Protected Netflix Videos in Real-Time Even though it's encrypted, Netflix uses variable bit rate (VBR) encoding, which leaves a distinct fingerprint: "we show that our system can differentiate between videos with greater than 99.99% accuracy."
Your Russian hacker name is your mom's maiden name followed by the last four digits of your SSN
None of the Above
Kevin Antony "You win Ikea. You win 🤔"

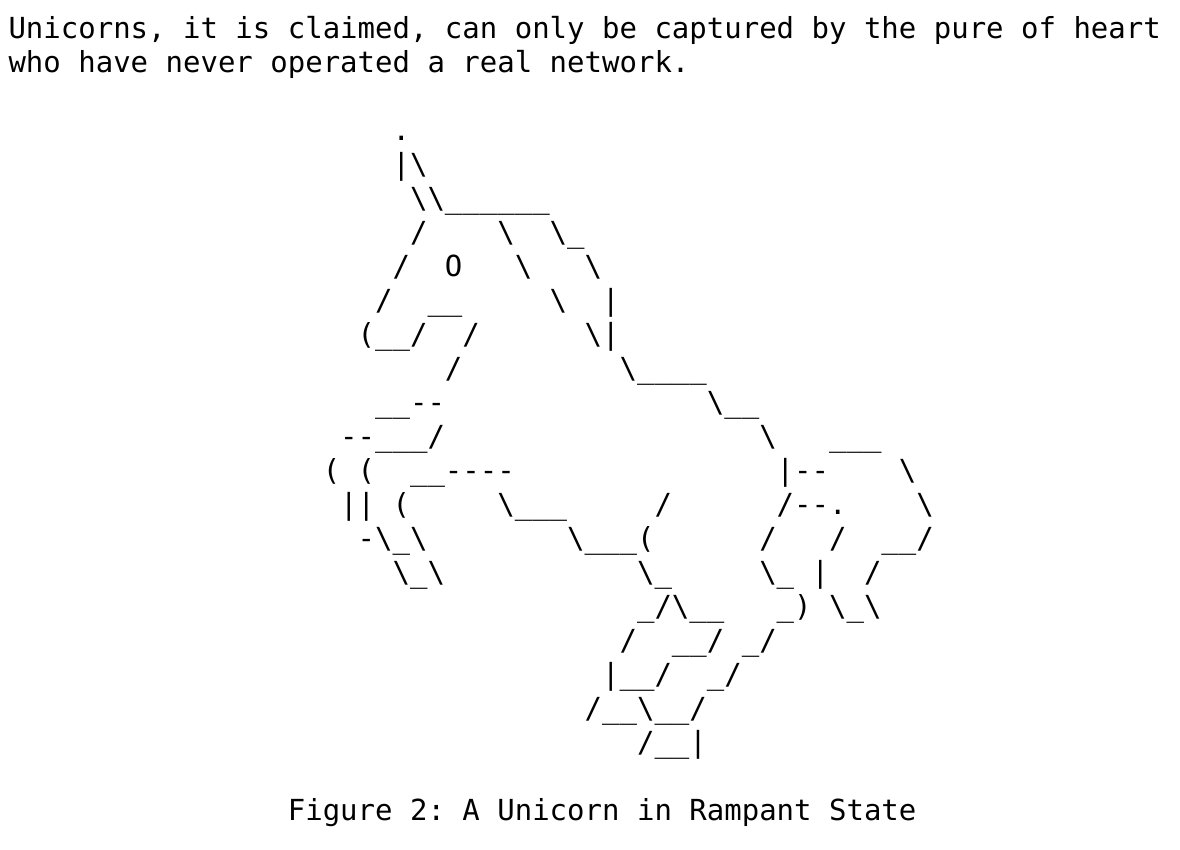
RFC 8140 The Arte of ASCII "This document attempts to address that yearning by demonstrating the full wonder of the natural world in vivid two-dimensional representation and a colour palette that would put even the august L. S. Lowry to shame."
AMP: Breaking News "The media have now almost completely lost control of distribution." Journalism relies on trust between the reader and the publisher, and you can't establish trust, if you can't tell publishers apart. Wither journalism in a world where all publishers look the same.
Ham Saladyce "I see cats have started writing for the telegraph"

Why Japan’s Rail Workers Can’t Stop Pointing at Things It looks silly, but it's the smart thing to do: "pointing-and-calling is known to reduce workplace errors by up to 85 percent."
Adam J Calhoun "Cats getting confused by optical illusions never get old"

Woman Who Drinks 6 Cups Of Coffee Per Day Trying To Cut Down On Blue Light At Bedtime That time, when the Onion wrote a story about me.
Nancy H. "When you're not paying attention..."
