Published
Weekend Reading — Walks like a duck …

Santero "Huh. Man with dogs in his pockets walking his duck, which has shoes on"
Design Objective
Atomic Design by Brad Frost Brad Frost explains atomic design, and how to apply its principles to your very own design system.
Designing for iPad Power Users If you are working on an iPad app, then please, yes and thank you.
The Problem with Liberal White Designers Jennifer Daniel:
Nothing has forced myself to reckon with what is important to me more than talking to people who disagree with me. I would challenge designers to talk to people who challenge them. People who don’t look like you, people who don’t think like you, people who make you angry and confused. It’s fucking hard but you can do it, or at least try.
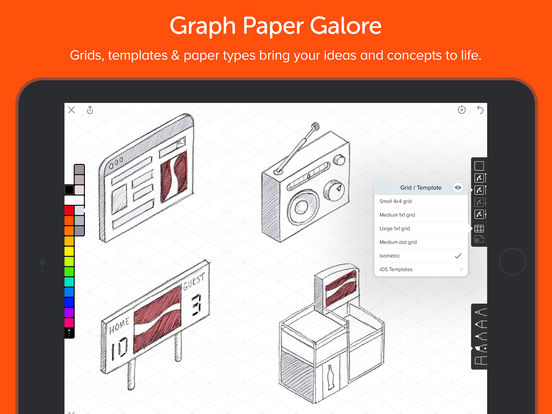
Linea - Sketch Simply Iconfactory's new sketch app for the iPad.
Tools of the Trade
We built a PWA from scratch - This is what we learned Caching gotchas and strategies, offline workers, add to home suggestions, and more.
Adventures with NPM or: How I Learned to Stop Shrinkwrapping and Love Yarn Mirrors my frustrations with npm. Be advised, Yarn is not bug free, not even close, but so far has proven more dependable than npm.
Magnet Cool little OS X app to help with window placements.

This browser tweak saved 60% of requests to Facebook On cache-control: immutable (shipping in Firefox) and the recent caching improvements in Chrome.
The future of the page cache Apropos, "Caching is the art of predicting the future, he said."
How to Prevent Gmail From Displaying An Image Download Button In Your Email If your email has an image above a certain size, Gmail will display an image download icon. Here are three techniques to disable this icon.

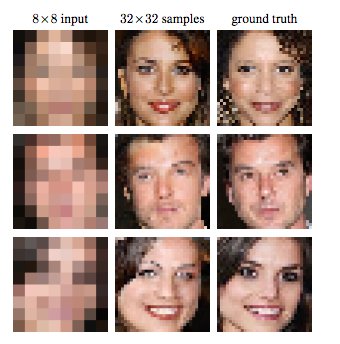
Pixel Recursive Super Resolution One step closer to CSI infinite zoom:
… by incorporating the prior knowledge of the faces and their typical variations, an artist is able to paint believable details. In this paper, we show how a fully probabilistic model that is trained end-to- end can play the role of such an artist by synthesizing 32×32 face images depicted in the middle column of Figure 1.
Finally an answer to the age old riddle. Which came first?
node -p "[ '🥚', '🐔' ].sort()[0]"
🐔
Lingua Scripta
Martin Kleppe: 1024+ Seconds of JS Wizardry -- JSConf EU 2013
The art of writing exceptionally compressed JavaScript.
Int64 & More Slides from Brendan Eich talk to TC39, about Int64, Uint64, and beyond.
Lines of Code
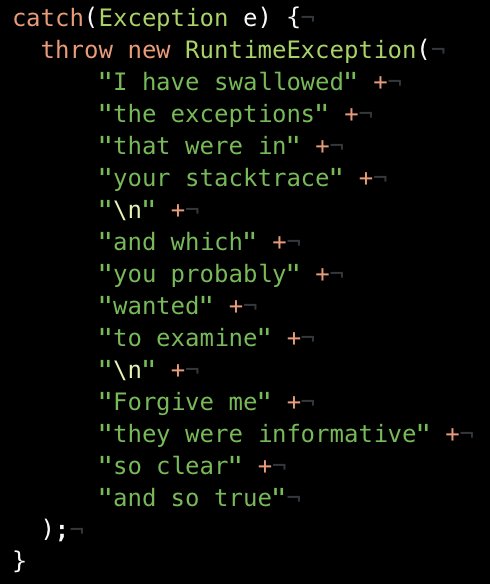
"What is technical debt?" Technical debt is hard to explain, but a picture is worth a thousand words

Sarah Mei In response:
It's not debt. It's clutter that eventually leaves you so little room to maneuver that you lose the game.
It's the same with software design. To avoid clutter, come in with a plan, but alter it to fit each new feature request you get.
Land Mines Preventing database landmines in your project: avoid shortcuts, be obvious, consider migrations.
Share domain knowledge 100x more often than you do tips on how to turn three lines of code into one line of code.
Devoops
GitLab.com Database Incident Or, why you must practice database recovery every so often:
So in other words, out of five backup/replication techniques deployed none are working reliably or set up in the first place. We ended up restoring a six-hour-old backup.
Peopleware
Managering in Terrible Times First, read Productivity in Terrible Times. Then follow these guidelines for supporting your team:
As managers, one of our responsibilities is to provide the safest workplace we can to those around us. This includes members of marginalized groups who are dealing with a rapidly worsening environment, folks who may be anticipating legal challenges, and people with families who are uncertain about their ability to keep their jobs and stay safe in their communities. How do we support our reports in this rapidly changing political environment?
Locked Doors
Coded A video series about the new generation of hackers that are rising up and fighting corporate/government surveillance.
Hotel ransomed by hackers as guests locked out of rooms Literally, locked doors. (Thanks andrew)
You're a victim with one word in 'Can you hear me?' phone scam TL;DR if you don't recognize the caller, send them to voice mail:
A growing "Can you hear me?" phone scam can make you a victim if you utter just one word: "Yes."
Certified Malice Now that HTTPS adoption has reached the tipping point, we have to reckon with the ease of acquiring intentionally deceptive certificates:
In my mind, this is a critical failing—while much of the objection is well-meaning (“We want a level playing field for everyone”), it’s extremely frustrating that we punish users in support of abstract ideals.

Quick reminder that "Potentially Unwanted Program" is antimalware-ese for "works pretty much like malware but has lawyers"
None of the Above
Mike Murphy "Why does my pasta need an app"

Something Happened: The origin of day-one patches The first story, in Ars Technica's anthology of "sad, funny, and weird workplace stories".
So far the main difference between my 20s and my 30s is all the fascism. No-one tells you how much fascism there will be in your 30s.
Bot Traffic Report 2016 On the web, no-one knows you're a bot.

Make America Bohemian Again The fascinating history of the Chelsea Hotel.
Suddi Raval "Take a minute to look at the brilliance of this street art."

