Published
Weekend Reading — The biggest function in the yard
@derekf03
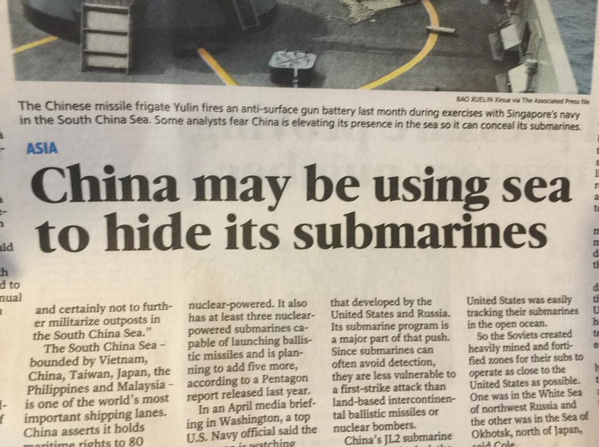
"Headline of the day."
This week we hide submarines in the sea; say death to bullshit; go retro with mechanical typewriter Vim; backdoor other people's JavaScript; pick the biggest function in the yard and refactor it; watch web ads go up in flames; hack in 6 inch heels; and find where the Minions are buried.
Design Objective
Death to Bullshit "This site and accompanying blog explore the themes of information, bullshit, and craft." And just for kicks, click the Turn bullshit on link (top right).
Tufte CSS CSS based on Tufte’s style, "known for simplicity, extensive use of sidenotes, tight integration of graphics with text, and carefully chosen typography."
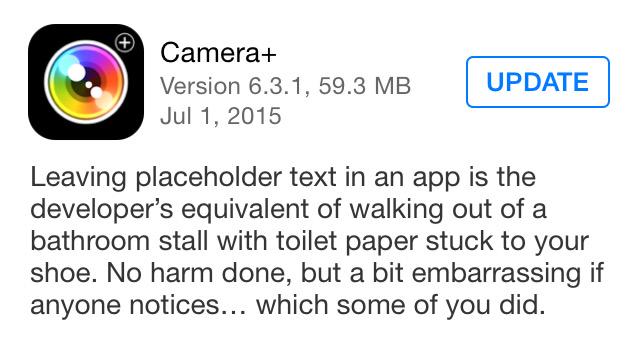
@jodyrodgers "One of the best app update descriptions of all time!"
Tools of the Trade
node-pip Import and use python packages in node.
Cooperative Scheduling of Background Tasks W3C draft spec for requestIdleCallback. Available in Chrome Canary.
10 Great Websites to Learn Coding Good starting points for beginners.
HystrixJS Inspired by Netflix's Hystrix module, "a latency and fault tolerance library designed to isolate points of access to remote systems … and enable resilience in complex distributed systems where failure is inevitable".
What does the OS X Activity Monitor’s “Energy Impact” actually measure? TL;DR an approximation based on CPU usage and process wakeup frequency.
Vim on a Mechanical Typewriter Retro all the way.
We need to talk about C++. Seriously.
Lingua Scripta
Logging variables via an ES6 tagged template Cool technique, combining ES6 tagged templates and abbreviated object literals.
backdooring your javascript using minifier bugs
The backdoor examples that I’ve illustrated are pretty contrived, but the fact that they can exist at all should probably worry JS developers. … Don’t minify/compress server-side code unless you have to, and make sure you run browser tests/scans against code post-minification.
Is “Isomorphic JavaScript” a good term?
- The technique of asssembling pages on either client or server. Here, “isomorphic” and “full stack” (as proposed by Rodrigo Medeiros) seem good choices.
- JavaScript that runs in all (or most) JavaScript environments, especially browsers and Node.js. Here, “universal” seems a good choice.
Lines of Code
Your Code as a Crime Scene This book looks interesting:
In our case the offender is code. So we learn techniques to identify patterns in the evolution of your code, how you’ve worked with it so far. That gives you the power to predict its future, to find the code that’s hard to evolve and prone to defects – our offenders!
While the half-life for software technologies is low, principles of good system design change more slowly, if at all. Experience matters.
OH: You can read code as a narrative in which a series of confusing and unpleasant things happen to data.
One sloppy file in a codebase may not seem so bad. But then people follow the patterns used in that file and soon you have 100 sloppy files.
when you start a new programming job you have to walk right up to the biggest function in the yard and refactor it in front of everyone
Adcrunch
@charlesarthur Watch:
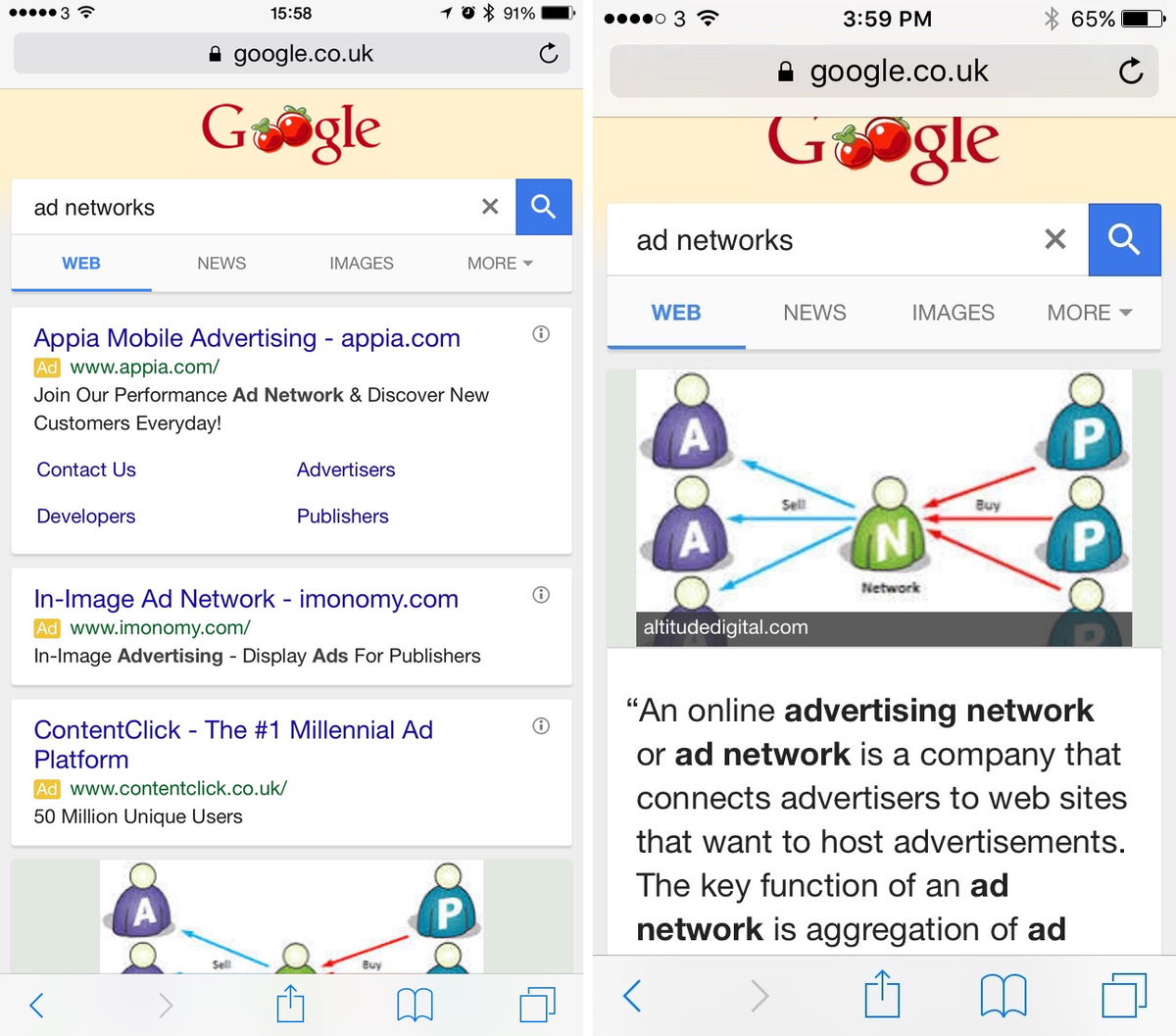
Left: Google search for "ad networks" on iOS 8. R: same on iOS 9 with @_CrystalApp content blocker. Well now.
Crystal Benchmarks Measure:
On average, pages loaded 3.9x faster with Crystal and used 53% less bandwidth. Just by having Crystal installed, I saved a total of 70 seconds and 35MB of data on these 10 pages.
Installing a Content Blocker on iOS 9 Public Beta Some assembly required (Xcode and such), but not too complicated, and in fifteen minutes you can run an open source ad blocker on iOS 9 beta.
Locked Doors
How security flaws work: The buffer overflow Understanding the common C vulnerability.
Pentesting Platform Shoes If you're going to wear 6" heels, they might as well carry a router, keylogger and lock-picking set.
Q2 2015 State of the Internet Security Report Released Akamai report about DDoS, Shellshock and XSS attacks, WordPress plugins, and TOR's growing usage in malicious attacks.
Your trial version of XKeyscore has expired. Please insert one country's metadata to unlock the full version.
Thank you @washingtonpost for posting the @TSA's master keys :) - All lock pickers #security http://www.heraldnet.com/apps/pbcs.dll/article?aid=/20141130/NEWS02/141139966
Peopleware
Software Developers’ Perceptions of Productivity (PDF) The difference between measured and self-reported productivity:
The survey results show that while most participants considered coding highly productive, there are several activities, such as meetings and handling emails, that are more difficult for developers to assess with respect to productivity …
Constructed Criteria (PDF) How we redefine objective criteria to support hiring biases:
Indeed, in Experiment 1, participants who exhibited the most pro-male bias in their hiring criteria also proved the most confident in the objectivity of their decision. They, perhaps, felt that they had chosen the right man for the job, when in fact they had chosen the right job criteria for the man.
Techtopia
@_youhadonejob "Sorry kids that's not a camera."

None of the Above
Told my friend's daughter that Kinder Eggs are actually Minion coffins. Now she's crying and I feel like Satan.
Leaving Everywhere Site that generates those "Why I'm Leaving [City]" essays using real US Census data.
We get it. You’re morally superior to the rest of us. Please stop writing posts on Medium about it and go to bed.
@conroyp As always, be wary of bias in data and lazy analytics:
Stories on Alabama being "most likely to cheat" state based on AM hack. Also 1st state in dropdown - wonder how many had 01/01/1900 birthday
@pauliewalnuts2 "Fucking hell"