Published
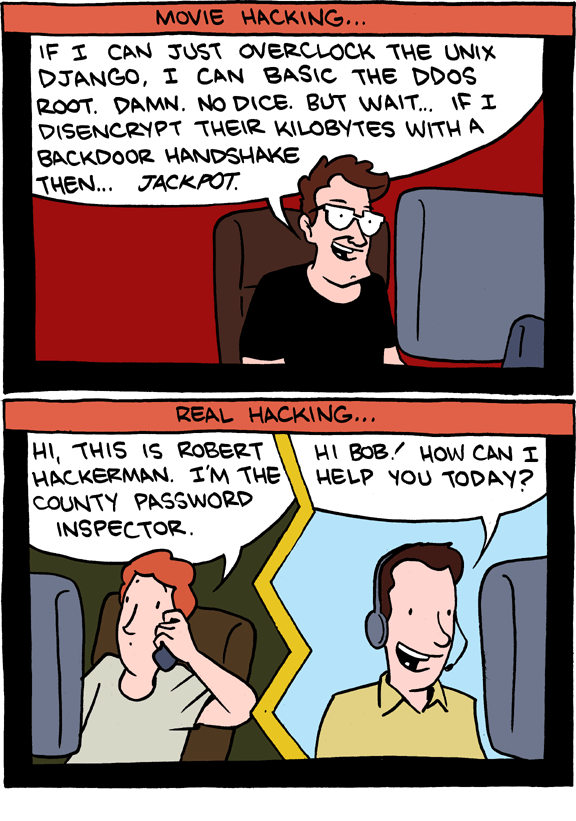
Weekend Reading — Real hacking
Design Objective
What Is a Card? Cards are more than just boxes of content with distinct border:
A card is a single unit of content or functionality, presented in a concise visual package. More advanced cards use that form to surface content or functionality from other apps, and allow users to interact with that content or functionality directly in the context of where a user encounters the card.
Think Your App Is Beautiful? Not Without User Experience Design This article strikes at the heart of a growing trend to separate UX from design:
The product gets uglier if it fails to meet user needs or becomes confusing. It’s like falling in love at first sight, then falling back out after a brief conversation. Your crush looks less attractive now; you can’t even recall why you were so captivated in the first place.
Tools of the Trade
JS Fest Mark your calendar, December 7th—13th, Oakland CA.
The Origin of Javascript with Brendan Eich It's a long read, but certainly worth it, of if you prefer, just listen to the podcast episode instead (same link).
Traceur with Erik Arvidsson Everything you wanted to know and were afraid to ask about Traceur and how to ES6 in JavaScript right now.
Tethr A killer iOS design kit, courtesy of InvisionApp.
CSS Shapes Editor for Chrome If you want to flow text around images, this is the cat's meow.
JSON Web Token (JWT) JWT lets you take some data, encode it as JSON, sign it with HMAC, and the result is a string you can safely add anywhere in a URL. Very simple, with implementations for all the major languages.
jquery-focuspoint A jQuery plugin for "responsive cropping". It lets you crop images so they fill up all available space, while maintaining focus on the image's subject.
LaunchRocket If you brew install services, LaunchRocket let's you start/stop them from a system preferences pane.
HTTP status 200-JUST-KIDDING-404
Locked Doors
Why Social Engineering Should Be Your Biggest Security Concern
- Obviously, never give out confidential information.
- Safeguard even inconsequential information about yourself.
- Lie to security questions, and remember your lies.
- View every password reset email with skepticism.
- Watch your accounts and account activity.
- Diversify passwords, critical services, and security questions.
Two Factor Auth (2FA) A website that helpfully lists popular web apps that support 2FA, and those that don't. Not surprisingly, banking, finance, and health are lagging behind.
Remind me to use this link next time someone says "bank grade security".
plan for a photo stealing Flappy Bird clone If an app asked for permission to access your pictures, would you click 'sure, why not'?
Notes on the Celebrity Data Theft Even if you don't give a hoot about celebrity nude photos, this is an illuminating read through the underbelly of the tech world. For reference, Meet the men who spy on women through their webcams.
Digital Attack Map This is just wow. A live map of DoS attacks happening around the world.
In a world of sensors, asking people to censor themselves where they can be recorded is approaching meaningless.
How does David Lightman in WarGames manage to hack a computer by dialing a number? A trip down memory lane.
His setup seems to be a telephone connected to a computer. When he dials another computer on the phone, he manages to gain access to it remotely.
Is this a realistic situation or just something done for effect?

Econ 101
Beautiful Illusions: The Economics of uberX No matter how much you'd like to believe it, should Uber win over taxies, it won't be all butterflies and rainbows, not by a long shot:
There are limits to markets, however, and the taxi industry presents an especially vivid example of that dynamic. We don’t need to have this discussion in the abstract — we actually have hard data.
Things Got Better, Slowly How confirmation bias affects our view of the stock market:
Everyone has heard of the crash of 1987, when the stock market fell more than 20% in one day. They call it Black Monday, and it will be remembered forever. But few cared about the 102% stock market surge that took place in the two years before the crash, or the 65% rally in the following two years.
This is why, as Fidelity found out, investors do best when they forget to trade in their investment account.
Why There Might Never Be Another Tech Bubble We're not in the midst (or start, or any phase) of a tech bubble. Sure there are examples of excess, but by and large, tech is acting all mature and well balanced:
- We’re more resilient about taking losses.
- We know a lot more about running Internet companies.
- Entrepreneurs are better networked.
- There is a better quality of accelerators.
- Ecosystems around the world are becoming viable and vibrant on their own turf.
Healthcheck
The Ways to Avoid Feeling Off During Workouts Got an off day? Pay attention what you eat and drink, how you sleep and think.
New Answers About Carbs and Fat QA on why carbs make you fat and specifically what fats to avoid.
None of the Above
Browser Plug-In Adds Huge Red Banner Above Sponsored Ads This looks promising.
The Forsaken: A Rising Number of Homeless Gay Teens Are Being Cast Out by Religious Families This is happening.
Book Publishing, Not Fact-Checking Most people believe that, because books are permanent, they're fact-checked. Not even a little.
What many readers don’t realize is that fact-checking has never been standard practice in the book-publishing world at all.

Visualizing Ferguson Let's not forget this happened, and will keep happening here in the US.
You. Machine. A short horror story as told by @BART_ebooks.


 )
)