Published
Weekend Reading — huge if true
Design Objective
A designer is a person who organizes choices.
The better you understand the range and implications of choices, the better designer you are.
Lessons Learned: Why Newton Swears by Plain-Text Emails TL;DR users respond when the email feels like a conversation.
The Line Of Death On the impossible task of designing UIs for secure browsing:
In web browsers, the browser itself usually fully controls the top of the window, while pixels under the top are under control of the site. I’ve recently heard this called the line of death:

Pwn All The Things Emails are just as hard:
Some folks asked why this is a bad email. So I annotated it.

Tools of the Trade
Dirty CSS Hacks for Responsive Emails With bloated markup, you can do a few interesting things with HTML emails.
CSS Writing Modes Explains how writing-mode: vertical-rl; works.
Color Supply In-browser color palette picker.
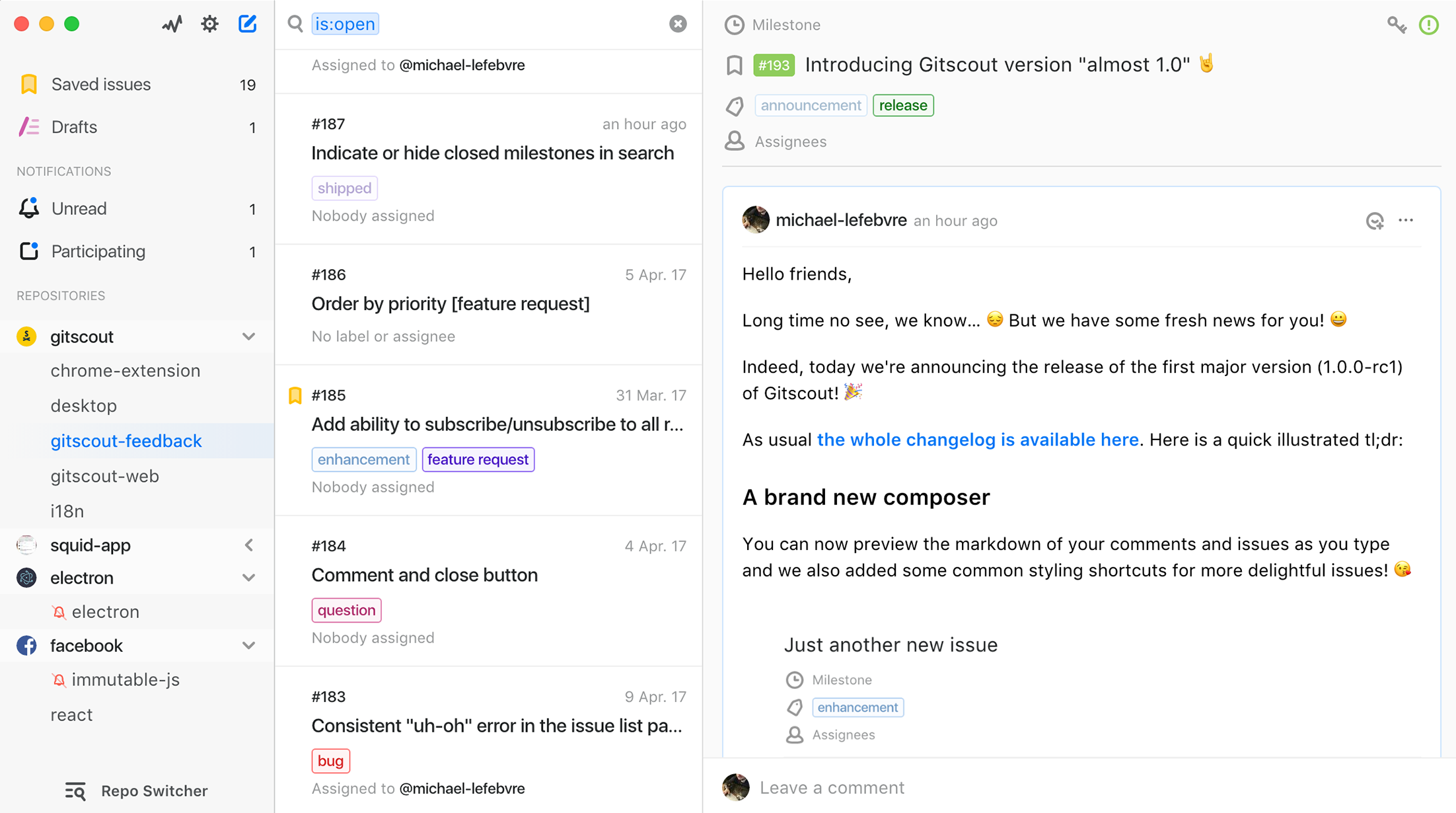
Gitscout Beautiful macOS app for managing your Github issues.
React or Vue: Which Javascript UI Library Should You Be Using? If you're not sure which to pick, start here.
Deep Text Corrector Using deep learning to correct grammatical errors.
nteract: Revolutionizing the Notebook Experience Desktop-based interactive computing application; think installable Jupyter:
Interactive computing applications allow individuals to create documents, like the one below, that contain executable code, textual content, and images and convey a computation narrative.
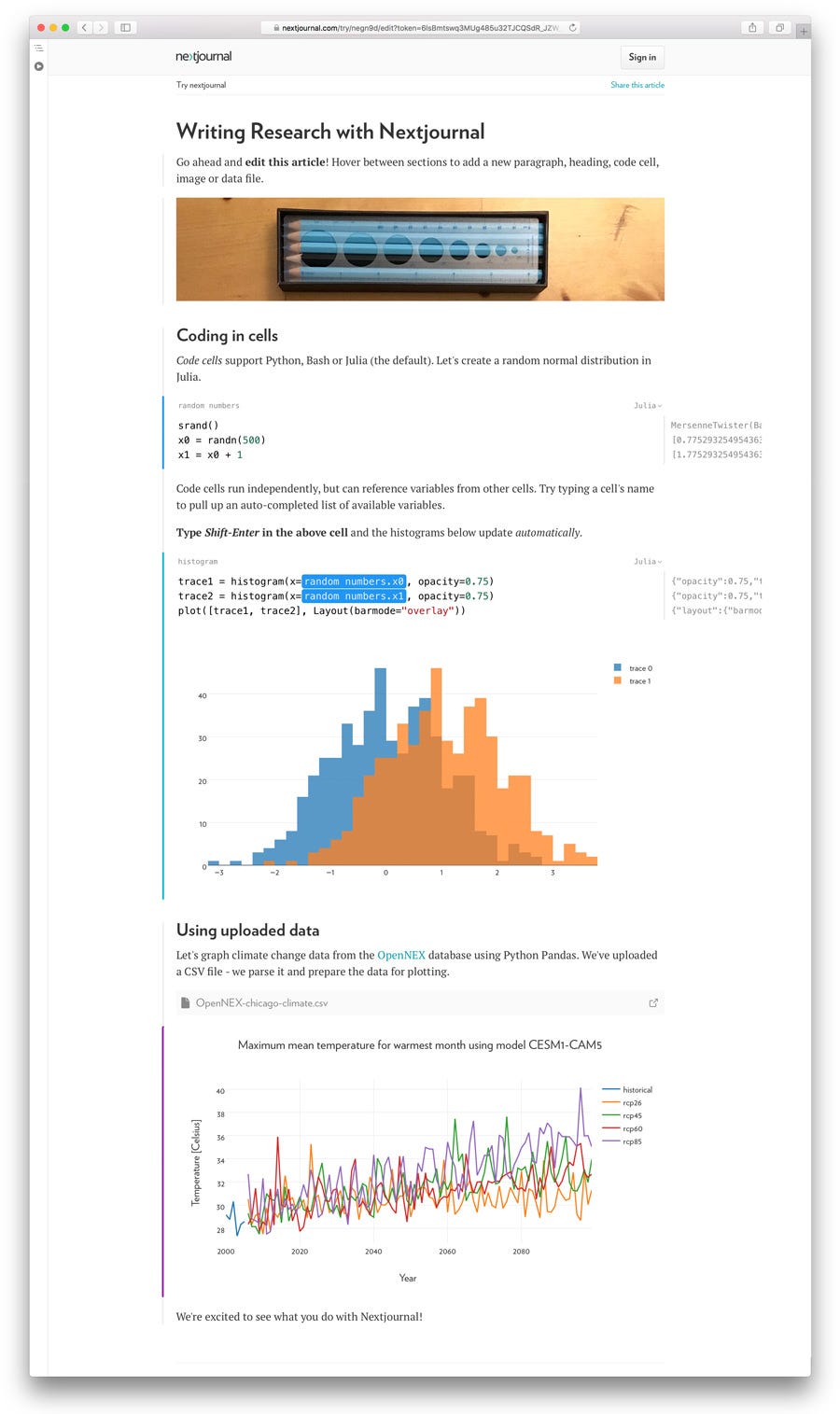
Introducing Nextjournal Another take on Jupyter, this time as a web app:
Today we’re launching a preview of Nextjournal: part writing tool, part interactive programming environment, designed for every stage of research from experimentation to publication.
Lingua Scripta
A Prettier JavaScript Formatter Re-format code instead of linting: "Prettier gets rid of all original styling and guarantees consistency by parsing JavaScript into an AST and pretty-printing the AST."
Brendan Eich TIL statement completion value:
It's not a return value, rather a statement completion value. Consider
for(var x=42; false;);which has no completion value.
ES proposal: import() An asynchronous version of the require function, to complement the static import statement.
Lines of Code
Single-letter names - a cautionary tale Sad and true:
I was fascinated that a graduate software engineer could not see the bug and disappointed that they had no interest to use meaningful identifier names. In our current education system, it takes a professional software engineer a good decade to realise that good identifier naming is important to code readability.
The Practical Dev This:
"First, solve the problem. Then, write the code." - John Johnson
The good news is that everything is statically typed; the bad news is that the only type is a String
I've never empathized with any fictional character as much as I do with this HorizontalScrollView...
Architectural
Take It to the Limit: Considerations for Building Reliable Systems Explains why limits — like message and queue size — should be built into the system, even if at times they feel inconvenient and arbitrary:
Unbounded anything—whether its queues, message sizes, queries, or traffic—is a resilience engineering anti-pattern. Without explicit limits, things fail in unexpected and unpredictable ways. Remember, the limits exist, they’re just hidden. By making them explicit, we restrict the failure domain giving us more predictability, longer mean time between failures, and shorter mean time to recovery at the cost of more upfront work or slightly more complexity.
Containers from Scratch Start here to learn what containers are, from the bottom up:
Often thought of as cheap VMs, containers are just isolated groups of processes running on a single host. That isolation leverages several underlying technologies built into the Linux kernel: namespaces, cgroups, chroots and lots of terms you’ve probably heard before.
Peopleware
An opinionated guide to writing developer resumes in 2017 I'm more likely to respond to a resume that follows the rules laid in this article:
The first rule is that you should always be truthful. Your next most important goal is to write a document that's easy to skim. If you work with web development, that should feel more or less natural to you.
Jessica Rose Asks, "How could/should one best screen for toxic workplaces before joining?" Hundreds of good replies in this thread.
Standing in the Shadow of Giants Open source and Manifest Destiny:
If we don’t change how we talk about open source, creators will continue to burn themselves out chasing an ideal they don’t really care about. New projects will continue to be excoriated for lacking novelty. We will continue to build the same ad hoc culture atop every greenfield we find.
Lullaby Language Words I'd like to eliminate from my work vocabulary:
Penny chimed in. “I get it. The ‘just’ makes it sound like there won’t be any problems. It discounts the difficulty.”
“Precisely. It’s what I call a ‘Lullaby Word.’ Like ‘should,’ it lulls your mind into a false sense of security. A better translation of ‘just’ in Jeff’s sentence would have been, ‘have a lot of trouble to.'”
Locked Doors
Matthew Green So about those implanted cardiac devices that can be programmed wirelessly:
But in case 24-bit RSA isn't bad enough, the manufacturers also included a hard-coded 3-byte fixed override code. I'm crying now. 9/
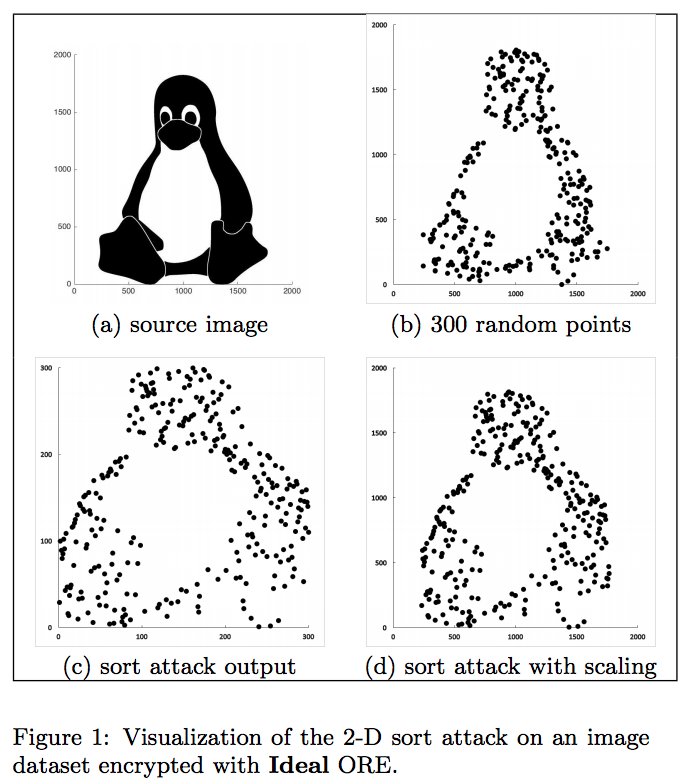
What Else is Revealed by Order-Revealing Encryption? Order-revealing encryption can be a desirable compromise — think encrypting a database but still being able to run queries — or an unintended security flaw:
CAA Records "CAA record is used to specify which certificate authorities (CAs) are allowed to issue certificates for a domain."
Patrick McCulley "Remote Command Execution #infosec"

None of the Above
TVs in the 1920s Had Bottle Cap-Sized Screens, With Just 30 Lines of Resolution

Boarding Group 2 is like the middle class in that, despite mathematical impossibility, everyone is in it.
Igal Tabachnik "huge if true"
Alexandra Erin "Then why does it change every day?"
Good morning! The #WordOfTheDay is immutable.
what if when you die you just see, "$1.99 to upgrade to pro"
The Swedes ditching desks to work from strangers’ homes Cool idea for remote/nomads: rent a desk at someone else's home.
The History of Email From humble origins as a file, through to FTP, to what we recognize today.

