Published
Weekend Reading — Vulnerability in a teapot

@stuartlogan Times Square with adblock enabled
This week we revisit the system font; we travel back to the 60's to fix a core dump; we discover the truth behind the ServiceWorker conspiracy; we go remote (on the job); agism is a thing; we hack into someone else's kettle; and we go flying like a superhero.
Design Objective
System shock A story of a 25-year-old font coming back with a vengeance.
Sweet new feature in OS X Mail.app reminds you when you forget to compose an email.
Tools of the Trade
chunkify "This is an API for getting long-running JavaScripts to periodically unblock the thread. The idea is to use timeouts to chunk up work and let the call stack unwind."
Xendo Search across multiple online accounts: Dropbox, Evernote, calendar, chats, etc.
Coolant Save battery life and keep your Mac cool by alerting you whenever an app takes over the CPU.
<input> I ♡ you, but you're bringing me down
There's more. I'm sure there's more. The thing is, browsers have had 21 years to sort out inputs, and they haven't even managed to agree on how to communicate "you haven't picked a file".
Incomplete List of Mistakes in the Design of CSS
Incomplete List of Mistakes in the Design of CSS Presented without comment.
Check Your DNS MX Records Do you know which servers receive your emails?
You probably want to do this year's YYYY audit soon, because 2016 starts on Dec 26 this year:
https://twitter.com/boredzo/status/549582777956323331
Fixing the core memory in a vintage IBM 1401 mainframe 4KB, that's how much memory this 60's era mainframe has. Also, ever wondered where the term "core dump" comes from?
Lingua Scripta
ECMAScript 6 destructuring gotcha Keep your destructuring expressions simple (for people to read), and you won't run into any gotchas.
The Art of Debugging Good stuff, for those working primarily in the browser.
The traversal order of object properties in ES6
Property keys are traversed in the following order:
- First, the keys that are integer indices (what these are is explained later), in ascending numeric order.
- Then, all other string keys, in the order in which they were added to the object.
- Lastly, all symbol keys, in the order in which they were added to the object.
Influences on ECMAScript 6 Helpful cheatsheet shows you which programming language claims "first!" to which ES6 feature.
Granted, ServiceWorker uses Promises, which are great. I love making Promises. Even if they're not fulfilled, they're hard to trace. Great.
Lines of Code
Me right now, getting too clever with my object-oriented metaprogramming #opsdev
Peopleware
You can either try to ignore this and accept the best people who will relocate for you, or you can explore how to make remote working patterns more effective. I think that organizations that are able to make remote working patterns effective will have a significant and growing competitive advantage.
18F’s best practices for making distributed teams work
18F has employees in every time zone, but GSA itself also has a fantastic telework policy. Thus, even if we were all stationed in Washington, D.C, there would still be a need for our “remote first” mindset.
JobSignal I don't know how representative this is of tech startups in general, but gives you a good idea of what to expect of AngleList (hiring and getting hired).
Maybe instead of killing Hitler, you could use the time machine to gain 10 years experience for an entry-level job.
Techtopia
People of color in tech Inspire the next generation, by highlighting PoC in the tech world; interviews with individuals, from startup CEO’s to junior web developers.
How Can We Achieve Age Diversity in Silicon Valley?
In Silicon Valley there is one underrepresented group in particular ... that not only has failed to enter this conversation, but is often regarded as anathema when it comes to headcount.
And that is people over 40. Or 45. Or 50, or 60. You know…old people.
The most disruptive technology of the last century is in your house
These technologies were so disruptive because they massively reduced the time spent on housework. The number of hours that people spent per week preparing meals, doing laundry and cleaning fell from 58 in 1900 to only 18 hours in 1970, and it has declined further since then.
How the Internet Has Changed Bullying
In some ways, when it comes to bullying, the Internet has made the world more rural. Before the Internet, bullying ended when you withdrew from whatever environment you were in. But now, the bullying dynamic is harder to contain and harder to ignore.
Locked Doors
Beware, connected ikettles can leak WiFi passwords The insanity that is IoT security:
“If you haven’t configured the kettle, it’s trivially easy for hackers to find your house and take over your kettle,” Munro says.
The Web Authentication Arms Race – A Tale of Two Security Experts Yes, authenticating people in a distributed environment is really this hard.
None of the Above
Adult-Sized, Street-Legal Version of the Iconic Little Tikes Cozy Coupe Car Now for Sale on eBay

This New Bell Helmet Is The Most Important Street Helmet In The Past 50 Years
The issue with current helmets is that they do nothing to stop the rotational or angular acceleration in a crash that causes the brain to spin, rotate, or shear inside your skull. ...
The idea being that, during an impact where the skull experiences rotational acceleration, the helmets has some flex and allows for some movement to help slow those rotational forces down.
In our culture, there are widespread assumptions:
- Boys aren’t going to like a book that stars a girl. (And so definitely won’t like a book that stars a girl + is written by a woman + is about a PRINCESS, the most girlie of girls).
- Men’s stories are universal; women’s stories are only for girls.
Painfully Accurate Drug Commercial Adulthood. There is no cure.
If you sensed something off about the story of the woman who sued her nephew, you were right
But her lawsuit makes perfect sense from a legal standpoint, and it seems those who rushed to judge have more to feel guilty about than Connell herself.
OS X El Capitan License: in Plain English
- Apple isn’t responsible for my hurt feelings for anything I see on the web.
- If I break any of these rules, this deal is over and I must immediately delete everything.
- The Capitan comes as-is.
- I can’t send it to Sudan.
- I can’t operate a nuclear power plant with it.
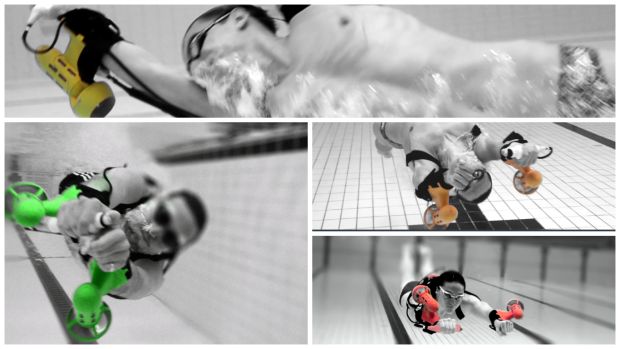
The x2 Sport Underwater Jet Pack Fly like a superhero: